Brad Bemis, MS, CISSP, CISA
| Principal Cybersecurity Strategist and Cultural Transformation Champion |
| Mental Health Professional and Prospective Ph.D. Candidate in Transformational Psychology |
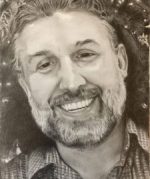 Hello, my name is Brad Bemis (MS, CISSP, CISA). I’m the Principal Cybersecurity Strategist and Cultural Transformation Champion at SecureITExperts. I’ve been working in the Cybersecurity industry for over 30 years now – and I truly love what I do.
Hello, my name is Brad Bemis (MS, CISSP, CISA). I’m the Principal Cybersecurity Strategist and Cultural Transformation Champion at SecureITExperts. I’ve been working in the Cybersecurity industry for over 30 years now – and I truly love what I do.
My engagement portfolio includes time spent in the trenches with Microsoft, T-Mobile, Lucent, Clearwire, Integra, Starbucks, Nordstrom, Expedia, REI, Boeing, SAIC, BBA, Airborne Express, Symetra Financial, Overlake Hospital, Jefferson Healthcare, and countless other small to medium-sized businesses, enterprise customers, and consulting houses. I’m also a U.S. Air Force veteran and have worked with a variety of military organizations and government agencies around the world.
I launched SecureITExperts, in 2012, as an Information Risk Management and Cybersecurity Consulting firm focused on providing strategic security management services to organizations of all types and sizes. While most of my work centered around governance, risk, and compliance, I’ve always been keenly interested in the root causes and conditions that lead to successful security breaches. Time and time again, I saw it come back to people – the people who build, implement, maintain, and use information systems. It always came back to the dynamic interrelationships that exist between people, technology, culture, and behavior.
In 2014, I began to incorporate things like simplicity, humor, and mindfulness into the security programs I was building. I also started to take a good hard look at human cognition, perception, and motivation – at how they influence the evolution and transformation of social systems. Ultimately, we are talking about transformation – transformation at the individual and organizational levels. We are talking about the rich, complex world of the human mind; how it thinks, perceives its environment, and engages the systems and structures that it encounters. What could be more applicable to exploring human risk factors?
This created a shift in my personal, professional, and educational pursuits. First, I started to work toward a master’s degree in education – which was exciting and very helpful, but it didn’t really tackle the hard questions I was asking. By 2018, I found myself going deeper into the study of psycho-social phenomena – really emphasizing how the whole human experience needs to be accounted for when we want to change behaviors. This led to several years of formal training in motivational science, applied behavioral analysis, counseling psychology, and life coaching – all while continuing my work as a cybersecurity consultant.
By august of 2021, I had earned a master’s degree in counseling, along with several related certifications. Now that I’m getting ready to start a Ph.D. in psychology, I’ve been devoting more and more of my time to finding new and novel ways to tackle the human risk factors present within organizational systems – how to educate and motivate the workforce, change patterns of thought and behavior, and reinforce a culture of security. I’ve always made awareness and training a central feature of my work, but at this point, it’s something more for me – it occupies a special place in my professional practice as a consultant.
Today my focus is on delivering strategic security management services that address root-cause challenges, enhance security service delivery, and increase the protective value of technology investments made. While I excel at each of these endeavors, my main passion is cybersecurity awareness, training, and cultural transformation work that is geared toward reducing human-factor risks and emphasizing the people-centric practices that are so critically essential to all aspects of a robust security strategy. This lets me combine two seemingly unrelated fields of inquiry under a single umbrella of “securing the human” in a unique and powerful way.
Below you’ll find a detailed breakdown of my background so you can get a better understanding of where I’m coming from and how I can benefit your organization as it seeks to explore and address these same challenges.
Introduction
Cybersecurity thought-leader with a 30-year track record of success in developing and implementing enterprise-class governance, risk, and compliance programs that balance the dual imperatives of enablement and protection.
Business and technology integrator with a deep background in network, system, and application security controls, including active defenses against current/evolving mobile, social, virtual, cloud-based, block-chain, and IoT threats.
Cultural transformation champion with an expansive, multidimensional emphasis on organizational psychology, functional behaviorism, and motivational science within a cybersecurity context that addresses human-factor risks.
Current Status
I am currently seeking a long-term opportunity focused on cybersecurity leadership, strategy, policy, process, awareness, training, and/or cultural transformation. I’m also open to roles that emphasize the management of technical security teams across all strategic, tactical, and operational domains. In the meantime, I’m still continuing to accept short-term cybersecurity engagements when time and opportunity allow – until employed in a long-term position.
Summary of Experience
[Governance] Built entire cybersecurity and information risk management programs from the ground up using framework components from CIS, NIST, SANS, ISO, HITRUST, ISF, ITIL, COBIT, COSO, AICPA, IASME, CIIP, IOTCA/IOTSF, ENISA, CSA-CCM, VERIS, and MITRE ATT&CK.
[Risk Management] Partnered with executive-level committees to measure risk appetite and set thresholds; formalized risk management processes, tools, and techniques; engaged in formal and informal risk assessments leveraging NIST, ISO, OCTAVE, FAIR, RAM, FRAP, and FIRM.
[Compliance] Conducted compliance readiness audits and directed ongoing remediation efforts to ensure conformity with HIPAA, SOX, GLBA, BSA, FINRA, PCI, CMMC, FISMA, FEDRAMP, DFARS, EGA, NERC, TSA, FERPA, ISO, PIPL, GDPR, CCPA, NYDFS, and state breach laws.
[Culture] Authored security principles, policies, standards, guidelines, and procedures in modular formats; designed and delivered structured security awareness, training, and education materials; drove behavioral modification efforts and cultural transformation initiatives.
[Technology] Produced certification and accreditation packages, system security plans, and POAMS for sensitive systems; aided development teams to incorporate security into the SDLC via AGILE, Waterfall, DevOps, and more; created and enforced system hardening standards for networks, applications, platforms, and devices; streamlined threat management and vulnerability remediation capabilities across the enterprise.
[Security] Evaluated third-party technologies, cloud service providers, and partner agreements; implemented and maintained cybersecurity tools, technologies, and services to reduce attack surface; administered and conducted penetration testing of systems, applications, databases, and networks; analyzed anomalous events and indicators of compromise against VERIS and MITRE ATT&CK patterns; spearheaded business continuity, disaster recovery, incident response, and digital forensic initiatives.
[Leadership] A passionate and skilled leader with expertise in team building, developing people, motivating others, and finding collaborative solutions – leveraging an extensive professional background that includes transformational psychology, clinical mental health counseling, life and career coaching, and teaching adult learners.
[Business] A rich history of running several successful entrepreneurial endeavors; including market needs analysis, product and service development, brand management and messaging, content marketing and communications, targeted advertising and promotional campaigns
[People] Early professional experience in human resources and personnel administration, emphasizing human performance management systems, organizational systems psychology, functional behaviorism, motivational science, team building and collaboration, policy and processes implementation, technical writing, and more.
[Community] An active, long-term contributor to the field of cybersecurity, involved in a number of professional associations, working groups, and projects – serving on association boards, giving lectures and presentations, spearheading advanced research efforts, and offering guidance and support in various online communities.
Industry Certifications
- Certified Information Systems Security Professional (CISSP) [Active: #24220, since June 2001]
- Certified Information Systems Auditor (CISA) [Active: #0331778, since July 2003]
- Certified Information Security Manager (CISM) [Pending: planned for Q1 2022]
- Security Awareness and Culture Professional (SACP) [Pending: planned for Q2 2022]
- Certified Life Coaching (CLC)
- Associate Business Continuity Planner (ABCP)
- Certified Lean Six-Sigma Greenbelt (CSSG)
- Cisco Certified Network Associate (CCNA)
- Cisco Certified Design Associate (CCDA)
- Nortel Networks Certified Support Specialist (NNCSS)
- CompTIA Certified Network Technician (Network+)
- Microsoft Certified Systems Engineer (MCSE)
- Microsoft Certified Professional plus Internet (MCP+I)
- Successfully completed 2 of the 4 CCNP exams (routing and switching)
- Military Technical Training Instructor Qualification and Certification
Formal Education
- Ph.D. Psychology, CIIS (Applicant for Fall 2022, August start)*
- Certificate in Teaching Adult Learners, UC San Diego, 4.0 GPA (2022)
- M.S. Counseling, Walden University (CACREP-accredited, 4.0 GPA) (2021)
- B.S. Information Technology, Minoring in Business Administration, University of Phoenix (2004)
- A.A.S. Information Systems Technology, Community College of the Air Force (1998)
- A.A.S. Personnel Administration, Community College of the Air Force (1998)
- Additional graduate studies in business and education
Specialized Training
- Technical Training Instruction
- Instructional Design
- Registered Behavioral Technician
- Behavioral Health Technician
- Mindfulness for Professionals
- Life Coaching
- The Consultative Approach
- Lean and Six-Sigma
- Project Management
- Military Leadership Training
- Nordstrom Leadership Development Track
- Seattle Institute for Management Studies
- Crisis and Trauma Counseling
- Dialectical Behavior Therapy
- Nonviolent Communications
- Cloud Security Management
- Computer Security Incident Handling
- Securing Microsoft Enterprise Platforms
- Computer Crime and Investigations
- Checkpoint Security Administration
- Introduction to Cisco Router Configuration
- Advanced Cisco Router Configuration
- Accelerated Nortel Networks Router Configuration
- Windows Architectural Design
- Windows Server Administration
- Exchange Server Administration
- HP Openview Network Node Management
- Introduction to UNIX
- Advanced UNIX
- Solaris Systems Administration
- Solaris Shell Programming
- Oracle Database Administration
- Oracle Developer Application Design
- Cabling for Voice and Data Networks
- Motorola Voice Communications
- Network Encryption Systems Administration
- Network Planning
- Network Systems Administration
- Various ongoing security lectures, seminars, and events
Memberships and Affiliations
- The Learning Guild
- American Counseling Association
- Florida Mental Health Counselors Association
- Mental Health Association of Central Florida
- Association for Contextual Behavioral Science
- International Coaching Federation
- Cloud Security Alliance (CSA)
- Information Systems Security Association (ISSA)
- Information Systems Audit and Control Association (ISACA)
- Computer Technology Investigators Network (CTIN)
- Agora Community – Seattle
- InfraGard Affiliate – Seattle
- Washington Software Alliance (WSA)
- King County Bar Association (KCBA)
- Pacific Northwest CISO Forum meetings and events
- Former Seattle CSA Chapter Secretary
- Former Puget Sound ISSA Chapter Secretary
- Guest Instructor for the Pacific Northwest CISSP Study Group
- Established the Security Program Management Forum for SecurityFocus.com
- A key contributor in multiple online cybersecurity forums and communities
- Maintained an information security portal and blog at www.secureitexperts.com
- Regularly consulted on issues of security awareness and training, policies and procedures, leadership and management, career development matters
Projects and Programs of Interest
- National Council for Workforce Education
- H-Layer awareness and culture certification initiative
- Behavioral Engineering as applied to cybersecurity
- The BJ Fogg Behavioral Model as applied to cybersecurity
- The Huang and Pearlson Model as applied to cybersecurity
- SANS research into cybersecurity and cultural transformation
- The NIST NICE Framework for defining the cybersecurity workforce
- Project Leader, CSA CCM 3.0 Mapping of ‘Jericho Forum Commandments’
- Project Founder, Independent Council for the Advancement of Cyber Security Ethics
- International Association of Awareness Professionals (IASAP) engagement activities
- Actively researching MITRE ATT&CK mappings and DBIR data analysis for behavioral targeting
- Currently developing an awareness matrix across all of the most common cybersecurity best practices and compliance requirements
Public Presentations
- Writing Security Policies People Will Actually Read
- How to Avoid a Mushroom Cloud
- Applied Mobile-Chaos Theory
- What ‘Hackers’ Do
- Preparing to Meet the Black Swan
- Data in Motion and the Wheels of Jeopardy
- Getting Your Head Right with Mindfulness-based Security
- Career Planning and Advancement in Cybersecurity
- The Business Case for Cybersecurity
- SMARTER Risk Assessments
- Toward a Standard of Due Care
- Intrusion Detection Systems From A to Z
- The Legal and Ethical Perils of Minimalist Compliance
- Panel on Security Culture
- Panel on the Future of Cloud Security
- Panel on Professional Development in Information Security
- Multiple additional in-house presentations for awareness and training purposes
Honors and Awards
- Chi Sigma Iota National Honor Society, 2018-2021
- Golden Key International Honor Society, 2019-2021
- National Society of Leadership and Success, 2019-2021
- John Levitow Leadership Award (USAF), bestowed in 1996
- Multiple awards and recognitions from employers and professional associations
Cybersecurity Work
SecureITExperts (June 2012 – Present)
Principal Cybersecurity Strategist and Cultural Transformation Champion
Owner and operator of a cybersecurity consulting firm. Engaged with clients like Starbucks, SAIC, and SeaWorld to build cybersecurity programs, conduct risk and compliance readiness assessments, lead remediation and technology refresh initiatives, establish data protection frameworks, develop awareness and training materials, respond to incidents, etc.
Clients include Starbucks, Teavana, SeaWorld, SAIC, Signature Air, Aspect Technologies, Webroot, REI, and others that are still governed by non-disclosure agreements.
Multiple Clients and Engagements (March 2000 – June 2012)
Cybersecurity and Information Risk Management Professional
Several years of combined FTE, consulting, and contracting work for clients like Microsoft, T-Mobile, Boeing, Lucent, Nordstrom, REI, Expedia, and more. Held roles ranging from systems security administrator to CISO. Led teams, built and managed GRC programs, conducted audits and assessments, enhanced protective security measures, wrote policy and process documentation, established awareness and training programs, taught classes and seminars, advised on cybersecurity landscape and threat reduction strategies, implemented and tested controls, responded to incidents, etc.
Clients include Microsoft, T-Mobile, Lucent Technologies, Clearwire, Comcast, Integra, Intelius, Moxie, ThruVid, Boeing, Nordstrom, REI, Expedia, Symetra Financial, Network Computing Architects, Airborne Express, U.S. Navy, Washington State Government Alaska Airlines, Western Peterbilt, Oki Developments, Diamond Parking, Columbia Hospitality, Silver Cloud Resorts, World Vision, Jefferson Healthcare, Overlake Hospital, Lake Forest Health, UW Medicine, Sunrise Services, Multnomah County, Washington State Employees Credit Union, School Employees Credit Union, Affiliated Associations of America, Port of Seattle, Puget Sound Energy, and others that are still governed by non-disclosure agreements.
United States Air Force (September 1991 – March 2000)
Personnel and Systems Security Management Professional
Served as a Personnel Specialist (3S0X1) for two years and then retrained into Communications-Computer Systems Operations (3C0X1). Managed personnel performance, readiness, and PERSCO functions; then system and security controls as the NCOIC of Wing Command and Control Systems (WCCS) and Theater Deployable Communications (TDC).
Clients include Air Mobility Command, Air Combat Command, Pacific Air Forces Command, and Air Force Special Operations Command with Joint Special Operations Task Force responsibilities supporting Air Force, Army, Navy, and multinational coalition forces performing covert wartime operations.
Mental Health Work
Awakening Into Life (2014-Present) – Teacher, Guide, Counselor, Coach, Mentor
The Meaningful Life Center (March 2021 – August 2021) – Student Intern, 6-month Clinical Mental Health Counseling Internship
Integrated Holistic Mental Health (November 2020 – February 2021) – Student Intern, 3-month Clinical Mental Health Counseling Practicum
Volunteer Work
Hospice Care, 1 year
Working with the Homeless, 5+ years
Mental Health and Wellness Advocacy, 3+ years
Red Cross Disaster Preparedness Volunteer, 2+ years
Additional Information
Currently in the application stage of pursuing a Ph.D. in psychology which emphasizes transformational potential, with a fall 2022 planned start – looking for a role that will allow my professional work and my academic pursuits to support and inform one another over the next several years.
Devoted to ongoing professional development activities in diverse areas that depart from traditional notions regarding ‘what works’ in cybersecurity – pushing boundaries and evangelizing innovative new approaches.
Deep emphasis on organizational and cultural transformation based on the principles of organizational psychology, functional behaviorism, and motivational science within a specific cybersecurity context.
A strong advocate for humor and levity within the domain of cybersecurity cultural transformation, drawing from evidence-based research that supports the use of humor to help facilitate change.
Previously held (and still eligible for) a Top-Secret Department of Defense security clearance with access to Sensitive Compartmented Information (TS-SCI).
Fully vaccinated against the COVID-19 SARS-CoV2 virus, including recommended booster shots – immunized with the Pfizer 3-dose series.